¡HI! If you want to propose us a project, send a mail to info@albatian.com


ALL INFORMATION ABOUT
BPM, PROCESS, R & D, TECHNOLOGY
The missing link
By Francisco González, Data transformations expert

Nowadays, an absolutely necessary condition for the sustained growth of a commercial company is how easy it exchanges information electronically with customers and suppliers. It is unthinkable today that a company that receives 100 orders and generates 100 invoices a day, takes orders over the phone or sends 100 envelopes by ordinary mail to their customers. As the business grows, the amount of staff resources required to handle such a lot of manual work increases proportionately.
Even if the order data arrives in an email’s body or the invoices are ...
Agile, the last trend in information technology
By Bernardo Ramos, IT security expert

Information Technology and fashion
New trends in Information technology appear often as a matter of fashion
New trends in IT use to emerge as oscillations between two extreme positions:
- Centralized / Distributed
- Simple / Complex
Around 1980’s IBM launched a computer series based on an architecture labelled “RISC” (as "Reduced Instruction Set Computing") RISC was the answer to the need of improving the old good IBM 360 complex architecture (CISC) that had been designed as a rich and complex instruction set processor to maximize the computing speed by ...
(Keep reading)Lean+SixSigma+TOC provide methods for continuous process improvement in BPM
By: Pedro Robledo, BPM process management expert
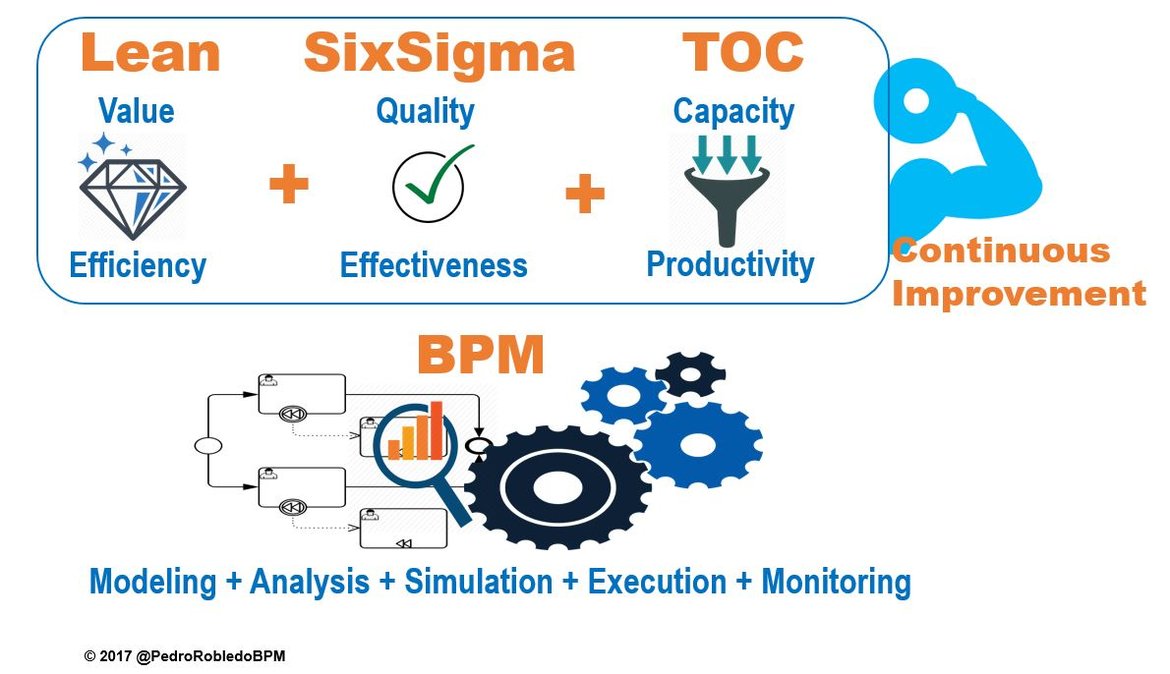
The discipline of process management (BPM - Business Process Management) makes continuous improvement of any organization possible, by allowing to manage the business processes in an efficient and reliable way. When looking for the quality of an organization we are referring to achieving a degree of inherent characteristics that meets certain requirements, needs or expectations, looking for cost savings, more revenue, greater productivity, greater profitability, greater customer satisfaction, improved branding, motivation and engagement of employees, flexibility and preparation for the future, better respond ...
(Keep reading)CYBERSECURITY
By Bernardo Ramos, IT security expert

Protect only what is needed:
- For its value
- Replacement / repair cost
The current situation: The truth is painful. The starting point for cybersecurity in at least 90% of cases is summarized as follows:
- You are spending too much money
- You are not well protected
Being well protected does not mean being 100% It is impossible to protect everything 100% Protection is inversely proportional to the inconvenience it causes to your employees, collaborators and customers. Except for a few exceptions You do not have a clear idea of the actual level of protection of ...
(Keep reading)PROCESS DIGITALIZATION IN DIGITAL TRANSFORMATION
By Pedro Robledo, BPM process management expert
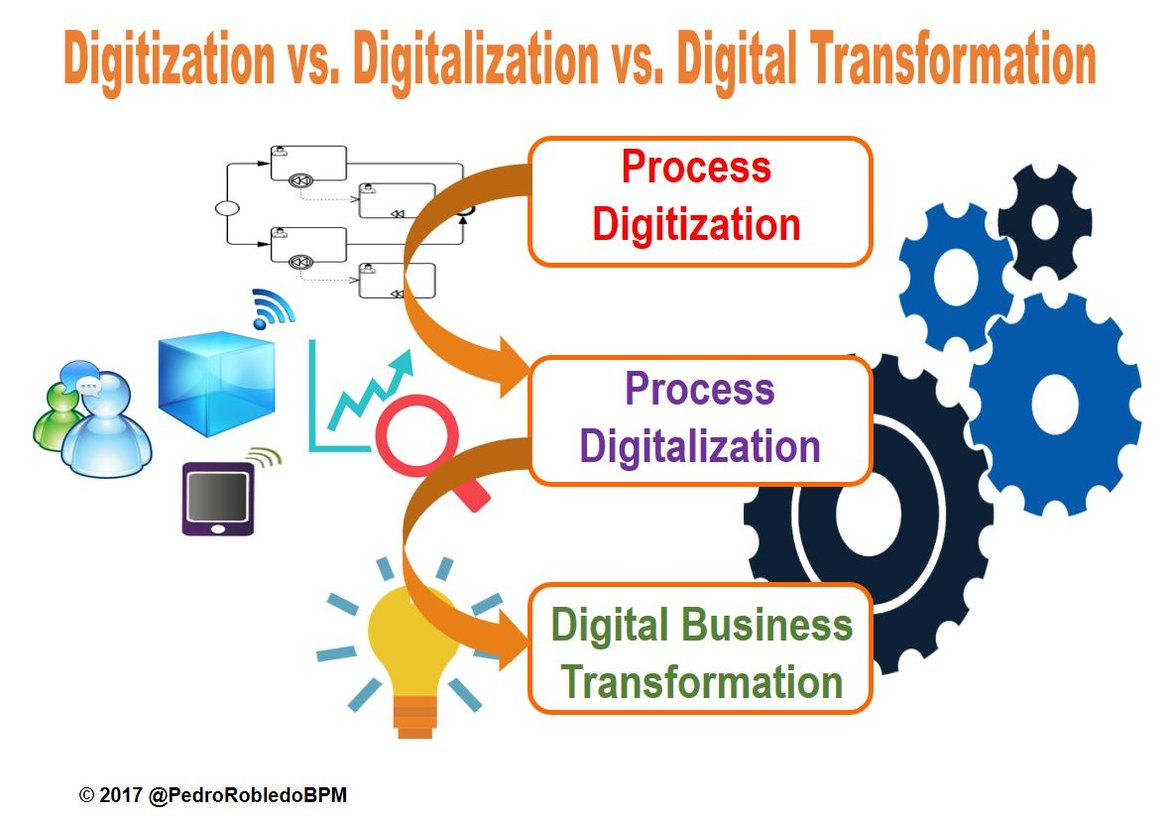
In a VUCA world (Volatile, Uncertainly, Complex and Ambiguous), companies are forced to innovate and adapt permanently to remain competitive and succeed. Mainly in the digital revolution where we find ourselves, where disruptive businesses appear that emerge even bypassing traditional barriers between sectors, changing the essence of traditional businesses and in many cases transforming products into services. This digital revolution is an opportunity, but it is also an obligation because customers are increasingly digital, have more information, compare, seek greater value and desire a more satisfactory customer experience ...
(Keep reading)










